What are the 9 types of Malware and how do they work?
Viruses
What is a computer virus?
A computer virus is a type of computer program that replicates itself by inserting its own code into other computer programs. Computer viruses generally require a host program (unlike a worm, for instance). When the host program is executed, the virus is also executed thus causing infection and damage.
How does a computer virus work?
A computer virus must contain a ‘search routine’ that locates new files that are worthwhile targets. Once located, the virus must contain a routine to copy itself into the program.
A ‘Trigger’, also known as a ‘logic bomb’ is the ‘compiled version’ that can be activated any time within a host file/program that determines when the malicious ‘payload’ should be activated.
The ‘Payload’ refers to the actual data which carries out the malicious purpose of the virus. Virus hoax is non-destructive but distributive.
What are the phases of a computer virus?
Dormant phase – This is when the virus has infected a target computer but is idle until the ‘trigger’ event which instructs the virus to execute. (Not all viruses have this phase)
Propagation phase – The virus starts multiplying and replicating – it can still be ‘dormant’ as this point. It has only begun placing copies of itself into other programs on a target’s computer. At this point a virus can change to evade detection from anti-virus software.
Triggering phase – The virus, having propagated, is now activated and will perform the function it was designed for. The trigger can be caused by a count of the number of times a copy of the virus has been made, or time based among other things.
Execution phase – the payload will be released. It can start its destructive tasks.
Worm

What is a computer worm?
Unlike a virus, a worm does not need a host program to replicate itself and spread. The advantage to this is that a worm is not restricted by a host program and can run independently.
Worms are more infectious than traditional viruses. They can infect local computer, but also servers and clients on a network. They spread easily through emails, web pages and servers.
What are the types of computer worm?
Email worms create outbound messages to all addresses in a target’s contact list. These messages can contain malicious attachments that can cause all sorts of problems (ransomware and further infection) when opened. Phishing is a common deployment technique.
File-sharing worms are disguised as media files. They copy themselves into a shared folder most likely located on a local machine. It will place a copy of itself there with a harmless name and wait to be downloaded by a user on the same network.
Internet worms infect web pages or popular websites with poor security. They are completely autonomous and can infect a machine to scan the internet for other vulnerable machines.
Trojan Horse Virus
What is a Trojan Horse Virus?
You know and love this horse! Just like its namesake, the Trojan Horse virus downloads onto a target’s computer disguised as a legitimate program thereby gaining access to deliver its malicious payload.
How does a Trojan Horse virus work?
Unlike viruses and worms, a trojan does not self-replicate and requires users to install it. However, that does not mean that an infected computer isn’t dangerous to other computers. The malicious software on the infected computer can be designed to turn that computer into a ‘zombie’, controlled by the hacker and used to have remote control of it. They can then use that computer to share malware across a network of devices (known as a botnet).
Trojans are often concealed in emails or ‘free-to-download’ files. Once installed it will execute the task it was designed to do which is often to gain backdoor access to a network, spy on users’ activity or steal sensitive data. Ransomware attacks are often carried out using a trojan.
Rootkits

What is a Rootkit Virus?
Usually this consists of a collection of software designed to give access to a computer by an unauthorized user. Rootkits are very good at masking their existence within a computer.
How do Rootkits work?
Rootkits can be installed through an automated process or can be installed by an attacker who has access to ‘root’ or administrator level access. Usually an attacker has gained this access exploiting a known vulnerability or password, both of which can be attained through other attacks. With this sort of access, the attacker can modify existing software (like antivirus) to remain undetected.
Removal of rootkits can be complicated to almost impossible and often reinstallation of the operating system is the only solution.
Kernel Mode – these run on the highest operating systems privileges by adding code or replacing portions of the core operating systems, including both kernel and associated device drivers.
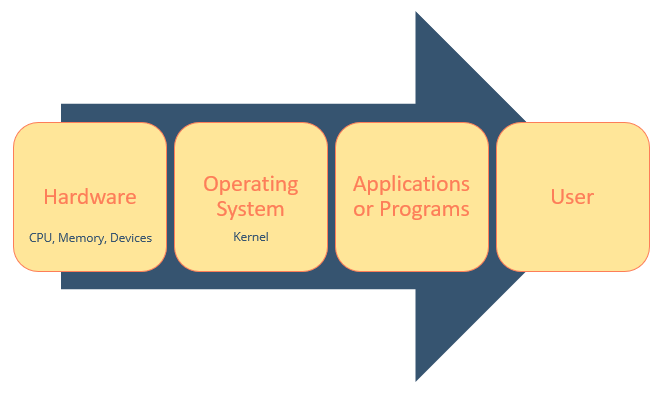
Bootkits – A variant of kernel mode these can infect startup code like the master boot record, volume boot record or boot sector and can be used to attack full disk encryption systems.
Firmware and hardware – These use a device or platform to create a constant malware presence in hardware (routers, network cards, hard drives, or system BIOS). Firmware is not usually inspected for code integrity so it’s a good place for a rootkit to hide. From here rootkits can seize data.
Backdoor Viruses

What is a Backdoor Virus?
Knock-knock.
Who’s there?
A malware that negates normal authentication procedures to access a system!
Backdoors are most often used to secure remote access to a computer or network by a cybercriminal. Backdoors can be delivered via rootkit, trojans, and worms. They can also be used to turn the target’s computer into a zombie or added to a botnet.
Backdoors are especially sinister because once the cybercriminal has gained access to the computer/network, and they’ve installed the backdoor, they will be able to keep accessing that device. So, even if the vulnerabilities are patched, the offending software removed, the backdoor remains untouched on the system.
Recently, given the COVID epidemic, criminals used fake Zoom installers (everyone working from home was installing all the various video conferencing apps) containing malware, one of which installed a backdoor that allowed bad actors to run routines remotely.
There are several type of backdoor intrusion techniques:
How do Backdoor Viruses Work?
Port binding – in a system without a firewall attackers can communicate with a computer port. Once the backdoor is bound to the port, attackers can freely communicate with the computer
Connect-back – With a firewall present, attackers can use a modified backdoor to check for available unprotected ports. They can then connect with a port that gives them remote access to the computer
Connection availability – Attackers can use backdoors to check for available connection and bypass intrusion detection systems.
Standard service protocol – They can use alternate protocols that aren’t typically detected like UDP instead of the more common TCP.
Keylogger Viruses

What is a Keylogger?
Is a type of spyware that tracks keystrokes on your keyboard. They record everything the target types, usually specifically trying to sniff out banking information. Otherwise, PIN codes, passwords, and other sensitive data are also up for grabs.
Many keyloggers have rootkit functionality meaning they hide very well in areas of the targets system where it can avoid detection.
There are many valid uses for keylogging technology. For instance organizations might use keyloggers to troubleshoot technical problems, families and business people might use them to monitor network usages without the users knowledge. Windows 10 has a built-in keylogger to improve typing and writing services.
How do Keyloggers work?
Software Keyloggers: This is a computer program designed to record input from a keyboard.
Hardware Keyloggers: Do not depend on software being installed as they exist on the hardware level. Examples of this are keyboard overlays, acoustic keyloggers, electromagnetic emissions, optical surveillance, physical evidence and more.
Mobile devices are also vulnerable to software keyloggers. These keyloggers are designed to take screengrab of emails, texts, logins.
Adware + Malvertising

What is Adware?
Adware generates online advertisements in the user interface of a particular software or on a screen presented to the user during that software’s installation process. This is a revenue generating process whereby the developer makes money by a) displaying the advertisement and b) a “pay-per-click” basis, if the user clicks on the advertisement.
What is Spyware?
Some of these advertisements also act as Spyware. The ad will collect and report data about the user, to be sold or used for targeted advertising or user profiling.
Some sources rate adware and spyware as nothing more than an irritant, while others indicate that it is as harmful as viruses and trojans.
What is Malvertising?
Malvertising and adware are two terms that are sometimes used interchangeably, though they are substantially different.
Unlike malvertising, which launches an attack via an infected ad, adware is a program that can be used to track a user’s web activity in order to display relevant or personalized ads.
All malvertising is considered malicious in nature, whereas some forms of adware are included in legitimate software packages. While adware often stokes concerns regarding data privacy and security, it does not allow cybercriminals to assume control of the system or alter, exfiltrate or delete data. Malvertising attacks may also execute an exploit kit, which is a form of malware that is designed to scan the system and exploit vulnerabilities or weaknesses within the system.
Though somewhat less common, it is possible to conduct a malvertising attack without having the user interact with the ad. These attacks include:
- A “drive-by download,” which exploits browser vulnerabilities to install infected files on the system while the user is passively viewing the ad.
- A forced redirect of the browser to a malicious site.
- Executing Javascript or Flash to display unwanted advertising or malicious content.
Bots/Botnets
What is a Bot/Botnet?
Malware bots are used to gain control over computers. Typically, malware bots are self-propagating and infect hosts with the intention of connecting to the threat actor’s server and letting them know another computer has been compromised.
When you have many bots serving one malicious purpose they are known as a botnet. A network of bots. Once the attacker has a large botnet at their service they can command the botnet to perform a malicious action such as launch a DoS attack, open back doors, data theft, malware distribution.
How do bot and botnets work?
There are some stages that help illuminate the functioning of a botnet.
Prep and expose – This is when the attacker exploits a vulnerability and exposes the target to malware.
Infect – The target is infected with malware and their device taken over
Activate – The attacker mobilizes infected devices to carry out attacks.
Mobile devices, wearable devices (smartwatches, fitness trackers .etc) and IoT devices (Internet of Things) can also become bots and be included in botnet attacks.
Botnet attacks are generally used to take down a targeted business’ website and then request payment for the attack to stop or simply to damage the business. Cyber activists use this method of attack to make a statement. Microsoft recently experienced a DDos attack against their Azure cloud network with bad actors trying to choke their network capacity.
Ransomware
What is Ransomware?
Ransomware is a form of malware (malicious software) that threatens to publish, block or delete a victim/s computer files, databases or applications. The threat actor will usually encrypt the victim’s data and demand a ransom fee in order to release the data back to the victim/s.
How does ransomware work?
The malware will encrypt or block the victim’s files using a randomly generated ‘asymmetric keys’. These are often called public-private keys. These encryption keys are uniquely generated for the victim and almost impossible to decrypt without the decryption key – which only the bad guy has. The bad guy only makes the decryption key available when the victim/s have paid up.
Types of Ransomware
Locker Ransomware blocks computer function all together. The target is denied access to anything on their computer but the good thing about locker malware is that it doesn’t target critical files.
Crypto Ransomware encrypts important data (documents, images, videos, databases etc.) Without payment, the attacker refuses to decrypt the files and the target (without adequate backups) faces losing all their data.
Major Canadian companies like CAMH, Western were affected by a ransomware attack on Blackbaud, Molson Coors and TTC most recently have all been targets for ransomware attacks.
